IoT Connectivity For Fleet Telematics And Management Technology
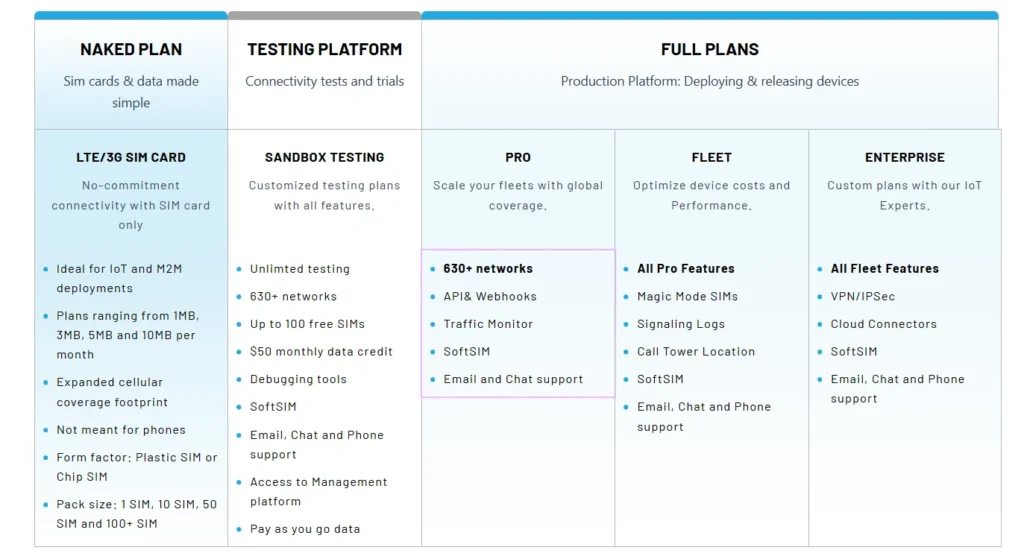
Fleet telematics is transforming the transportation industry, providing businesses with essential tools to optimize operations and maintain a competitive edge. With IoT connectivity for fleet